While homeowners consider wireless cameras as a way to protect their homes and loved ones, one of the many ironies is that these cameras can be less secure and used to commit crimes such as invasion of privacy and even assist in burglaries!
Most surveillance cameras today are WiFi-enabled simply because they are cheaper and more convenient to use. However, WiFi is known to be susceptible to hacking if it isn’t configured correctly, and that includes WiFi cameras. Nowadays, skilled hackers can easily break into your internet-connected devices and get access to your security cameras if you haven’t secured them properly.
We’ll cover why it’s important to secure your security cameras (hopefully, you know this already), the most common security camera hacks, and how to prevent security camera hacking.
Why It’s Important to Secure Your Cameras

One of the most disturbing thoughts is that hackers can get access to your wireless cameras and watch your family. They could get live feeds from close by or a few miles away while you’re at home, at work, or on vacation.
Hackers can basically do almost anything they want once they get access to your cameras - monitor you and your kids, take away your sense of privacy or even play with your connected devices such as your thermostat or lights.
And if they’re nearby, hackers can determine when is the best time to break into your home to steal your valuables. Or, they could use the opportunity to record your passwords and bank details to break into those accounts.
For these reasons, it is best to know how these hackers get access to your cameras and learn how to protect your devices from being hacked.
Most Common Security Camera Hacks
DISCLAIMER: The information provided in this post is for educational purposes only. The goal of this article is to spread awareness, provide readers about information security, and teach our readers how to protect themselves against these hackers.
Access Security Cameras Using Default Passwords
Any individuals that want to hack your IP cameras can simply search for your IP address online to access information about your devices and try default passwords to log in. To make setup easy, many camera installation instructions encourage insecure ways to bypass your firewall to the outside network to make viewing footage on your phone while you’re away easier.
But, that approach can leave your network vulnerable.
Search engines such as shadon.io and angryip.org allow anyone to obtain signature information to access your devices or the entire security system.
Ideally, the camera should still keep others out. But since manufacturers often use similar default passwords, the default state of the camera is very insecure. Once that camera is exposed to the internet during the initial setup, no firewalls or network protocols can help you if you fail to change the default passwords. The lesson is to never overlook that step whenever you decide to buy a new IP camera for your home security or when you reset a stubborn camera when troubleshooting.
Finding the User ID
Knowing your email, username, and phone number used for registering a camera is enough for hackers to know your user ID. Knowing this information allows them to reset your account, change your password and email, and manipulate your devices or your whole wireless security devices.
Using IP Camera Exploit Tools
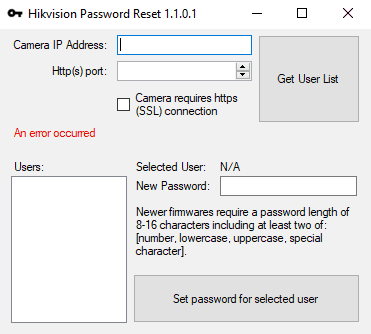
Let’s say that you’ve changed your default username and password. Hackers may still be able to access your security cameras by using a camera exploit tool, especially if your device has security problems (and practically all of them do at some time or another).
Exploit tools are used to automate the hacking process by running the software on a computer or laptop to look for a camera connected to your local network or over the internet. To use the tool, hackers still need to know your security camera information to configure the software. Cameras that are exposed to this security vulnerability are often the ones who failed to update their firmware.
So, it’s important to purchase from a company that will provide regular updates!
Do you think that a $30 camera from a Chinese company on Aliexpress will do that? Don’t count on it!
Using Command-Line Access on the Network
To get information about your security camera, hackers can use command lines so that they can get access to your device and even take a screenshot.
For instance, you can determine the details of a Hikvision camera (given that its firmware is not updated) using the following command:
<<camera IP>camera IP>:<<camera port>camera port> System/deviceInfo?auth=YWRtaW46MTEK
You can also take a screenshot from the camera without the need for any authentication using the following command:
<<camera IP>camera IP>:<<camera port>camera port> onvif-http/snapshot?auth=YWRtaW46MTEK
Take note that this information is provided for educational purposes only. You shouldn’t use these to hack cameras that are not yours!
Hacking Weak Passwords
If you’re using a password that’s easy for hackers to guess, then you’re putting your devices at risk. Somebody could simply try different passwords, especially if you are using common words or the hackers know some of your details (like usernames, emails, etc). Trying your luck by guessing multiple passwords could be a tedious task!
But, there’s software design just for the task - to process hundreds or even thousands of possible passwords per minute - then you can increase your chance of getting the correct one quickly!
Hackers can use Hydra for Windows or Linux to have their password file processed and use the following command:
hydra -s 88 -l admin -P /root/desktop/pass.txt -e ns <<camera IP>camera IP>Fortunately, a lot of modern security cameras today will not allow anyone to use this method since they can be blocked by the device after multiple login attempts.
You may want to look into the security features that your prospective camera uses before you purchase.
Security Vulnerability of Mobile Phones

The best thing about using wireless security cameras is that they can help you monitor your home and loved ones remotely through an app on your smartphone. These cameras often have their own dedicated apps to let you view live footage directly to your phone.
However, this can create an access point to hackers if your smartphone isn’t secure. Many people don't invest in securing their smartphones like they do on their desktop computers/ laptops, making their device vulnerable. Make sure your phones are secured, otherwise you may be exposed without you even knowing it!
Here's a video showing how unsecured cameras can be easily hacked:
How to Know If Your Security Camera Is Hacked
It could be difficult to tell whether your security camera has been hacked or not. There are simple ways to determine whether your security has been compromised, however, these may not be enough. The best way to protect yourself is to avoid any of these from happening in the first place.
We’ve summarized some of the telltale signs if your security camera has been hacked below:
Some of your camera functions are disabled
Modern security cameras have features to set it to record for a few seconds when there is motion or schedule it to take pictures of certain times within the day. However, if some of these features have been changed or disabled without an explanation, then someone could have accessed your network and seized control of your device.
Your camera functions oddly
Have you noticed your camera turning on or off by themselves, or moving abnormally? Then someone could be accessing your camera and controlling it remotely without you knowing it!
Unusually poor or slow performance
Cameras have limited memory - it’s one of the reasons why you don’t want your camera to record live footage for 24 hours! However, if a hacker has access to your camera, he could take it over to monitor your whereabouts or set the device’s CPU into overdrive. This could consume a lot of memory, slow down your device, and potentially disrupt other network traffic and devices in your home too!
Strange IP recorded into your system’s IP history
One of the simplest ways to determine if someone else is getting access to your devices is to check the IP history of your network. If there’s a strange or unfamiliar IP logged into the system’s history, then you’ll know that somebody else has accessed your network.
Be sure to check your router’s logs periodically to keep track of new devices and make sure they’re only the ones that you brought home!
How to Secure Your Cameras Against Hackers
Now you know that there are many ways hackers can access your security cameras, then what are the best ways to protect your devices against hacking?
Change Your Camera’s Default Password
Never use the default password for your devices! It is highly recommended that you change the default password with a mix of random characters, uppercase and lowercase letters, symbols, and numbers. Never use passwords with personal information about you or passwords that are commonly used.
Use A Password Manager
You can set up a password manager that can generate strong passwords for your accounts. This program can securely store and automatically insert passwords into your login prompts so that you can use strong, different passwords for each device, and access them all using a single password.
They even have versions that you can run locally, that don’t rely on a cloud service.
Make Sure Your Camera’s Firmware is Updated
A lot of manufacturers of modern security cameras routinely release firmware updates to ensure that your devices are always protected and fixing vulnerabilities. While some cameras automatically download and install the updates, some cameras may require you to install the updated firmware yourself.
So, be sure to schedule a task to check periodically, say every time you change the batteries in your smoke detectors. :)
Use Two-Factor Authentication For Your Devices
You can add an extra layer of security to your devices by adding the two-factor authentication method if it’s available. This works by having the camera company to send you a passcode via your chosen platform (text, email, call, or authentication app) whenever you log in to your account. This way, if a hacker succeeds in cracking your password, he won’t be able to access your device unless he also gets access to the passcode sent by the camera company.
Secure Your Wireless Network
Whether you have wireless cameras at home or not, this step should never be overlooked and should have been done in the first place. Otherwise, you are exposing your wireless network to vulnerability and giving hackers an opportunity to access all of your devices. Your best defense is to use WPA2 (Wifi Protected Access 2) technology so that your network passwords are encrypted. As of today, WPA2 is the strongest encryption program to protect your network from hackers.
Use VPN

A VPN or virtual private network allows you to connect to a remote server whenever you are connected to the internet, making it one of your best defenses against hackers.
Normally, your local network and computer can be easily traced back with a through-line whenever you are connected to the internet. Using a VPN, this private server provides a buffer between you and the internet. The through-line gets distorted which makes it difficult for hackers to access your network and devices.
Enable Your Firewalls
Firewalls act like watchtowers that monitor the incoming and outgoing traffic going to and from your network to the internet. The firewall filters the information coming in and out using a set of rules to block malicious attackers. These rules have been updated over the years and have become more and more complex in order to keep hackers at bay.
And often, you’ll have to open up a particular port to a device to get it working the way it was designed. But, the small inconvenience is worth the effort to keep hackers off of your network!
Here's a video for more tips on how to secure your security cameras from hackers:
Tips Before Buying a Wireless Camera
Buy a camera from a trusted company
It is always tempting to buy a security camera that’s cheap or on sale but the brand is either unknown or doesn’t come from a reputable company. Is it really worth the risk? Your camera should protect your home and should never compromise the security. Some cheap cameras can be easily hacked, and they don’t come with a lot of support, things like firmware updates to fix bugs and enhance security features.
Buy a camera that supports easy firmware updates
Manufacturers of modern security cameras ensure that they are able to provide the optimum protection of their users and are always a few steps ahead of any schemes devised by hackers. Make sure that the camera you purchase has support for firmware updates and a proven history of fixing bugs in their devices.
Buy a camera that supports 2FA (two-factor authentication)
We mentioned above that having 2FA for your devices can help discourage hackers from accessing your cameras. However, only a few camera companies offer 2FA. As of the time of the last update, the popular brands that have this feature are Nest, Ring, and Amazon.
Know which camera works best for you
Security cameras can be wired or wireless, and we have already seen that each of these have their own pros and cons. Wired cameras are difficult to install but offer more security than wireless cameras. On the other hand, wireless cameras are cheaper and more convenient to use. You can have the option to connect your cameras on the local network only to increase your security but won’t be able to use the cloud to access videos when you’re away from home. As a homeowner, you need to consider these pros and cons and determine which will work best for you.
Wrapping Up
Securing your security cameras is as important as securing your home. After all, these devices are supposed to protect us from criminals but, without proper security, can be used against us. We hope you find this article helpful to protect yourself and your loved ones.
Don’t forget to share this post with your family and friends! If you have any other thoughts or suggestions, leave your comments below!
References
Hi, I’m Christy, and I’m an electronics engineer by profession. I have taught in a university for 2 years while pursuing my master’s degree in cognitive radio and worked for a company to develop wireless medical devices. Currently, I’m doing research for a doctorate degree in engineering using a wireless sensor network for smart agriculture. I’ve been active in our local IoT community, IoT Cebu, where I participate in conducting talks about Arduino, Raspberry Pi, and DIY home automation using Wi-Fi and ZigBee devices.

